DAC General Configurations
Starting with QueryPie version 10.3.0, Database Access Control (DAC) related settings, previously located under Administrator > General > Security, have been moved to General > Configurations within each respective service menu that utilizes DAC.
Database Access Control Configurations
This section describes how to manage settings that apply to database access control.
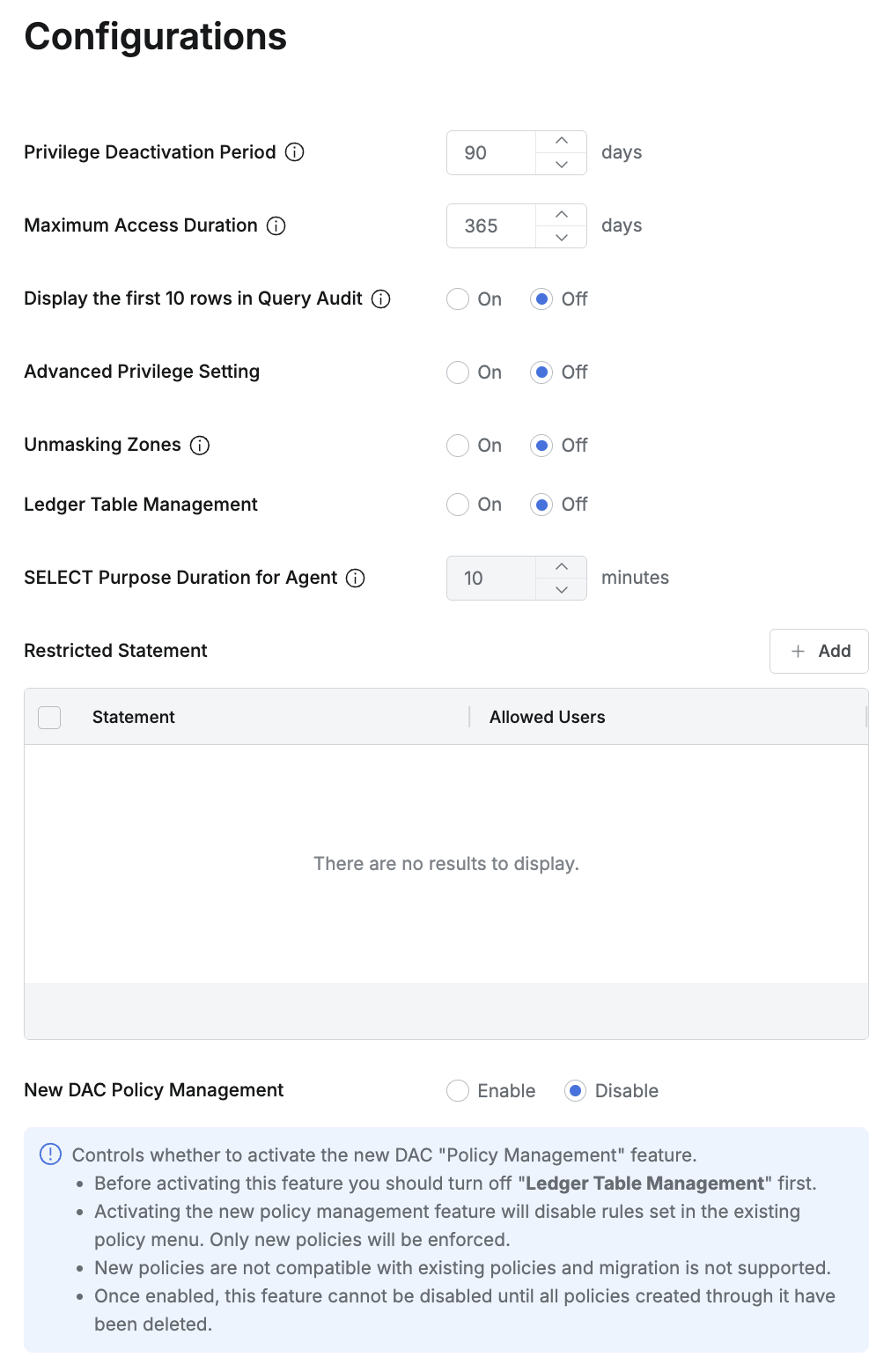
Privilege Deactivation Period : The period of non-use after which a database privilege (Privilege) is considered for deactivation due to long-term inactivity (Default : 90 Days).
Maximum Access Duration : The maximum duration for which a privilege can be requested or assigned.
When submitting a DB Access Request, an expiration date exceeding this specified maximum period cannot be set.
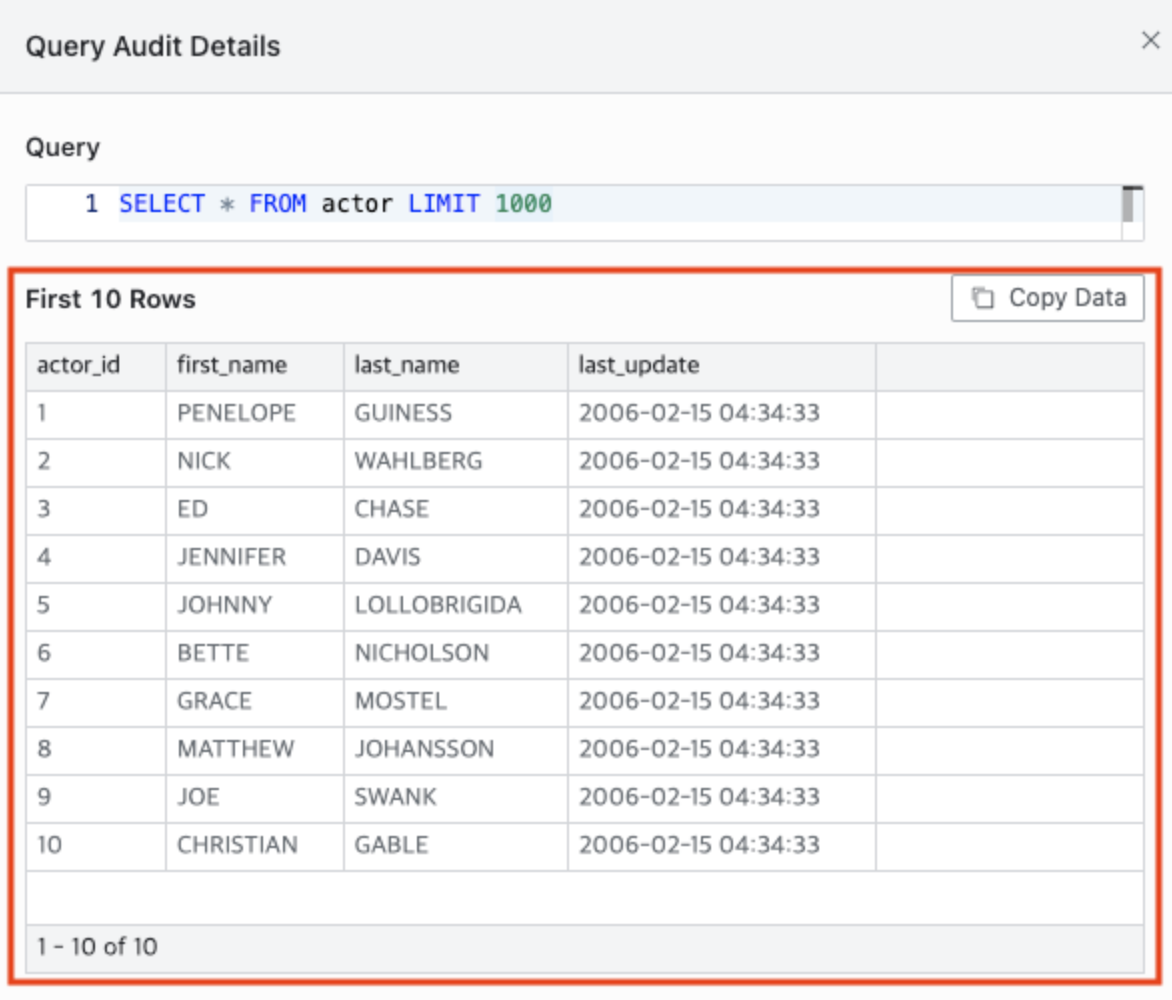
Display the first 10 rows in Query Audit : Configures how the results of SELECT statements are displayed within the Query Audit (Default: Off. If set to On, instead of displaying the full results, only the first 10 rows will be shown).
Advanced Privilege Setting : Enables account control based on specific privileges (Default : Off).
If set to On, a Privilege Settings tab will be displayed at the bottom of the Connection Details page.
For detailed information, refer to the Privilege Setting documentation within the DB Connections section.
Unmasking Zones : This setting allows users who are authorized to view unmasked data (either through an Unmasking Request or by being registered as an "allowed user" in a masking policy, thus exempting them) to view data in an unmasked state only if they are accessing from specified IP addresses or ranges (Default : Off).
For a detailed explanation, refer to Unmasking Zone documentation.
Ledger Table Management : Enables or disables the Ledger Table Management feature. This feature allows specific tables to be designated as "Ledger tables," for which Workflow approval and mandatory reason input for operations can be enforced (Default : Off).
Select Purpose Duration for Agent : Configures a duration during which users connecting to a database via a proxy (e.g., through a 3rd party tool) do not need to re-enter a reason for accessing data that requires mandatory reason input. This setting is applicable only when "Ledger Table Management" is set to On (Default : 10 minutes).
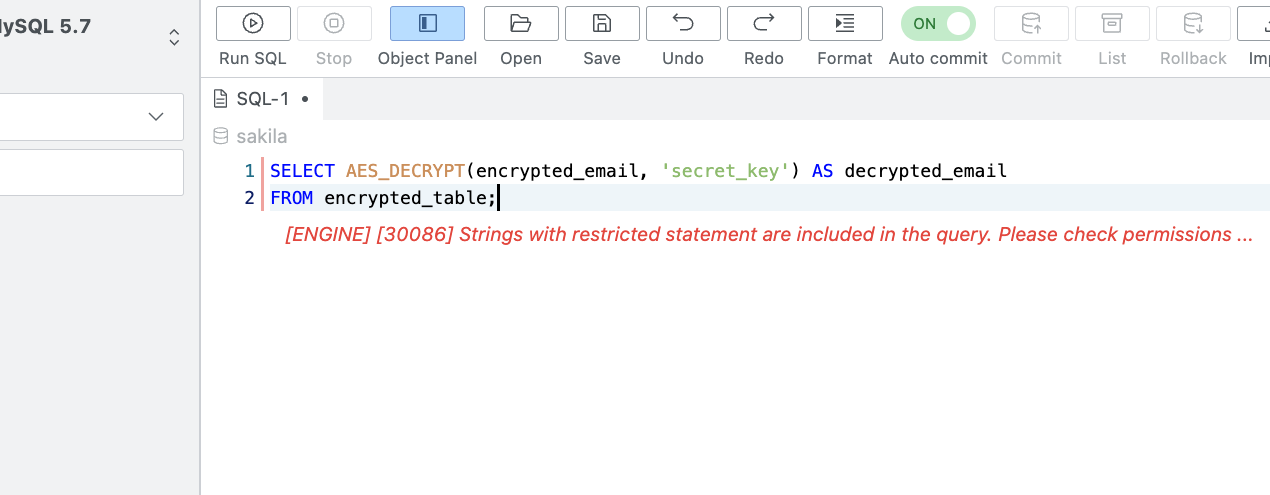
Restricted Statement : Defines query strings that are restricted from execution.
Statement: Enter the string (case-insensitive) that, if included in a query, will cause the query execution to be restricted.
Allowed User: Specify users who are permitted to execute queries containing this restricted statement. Multiple users can be selected; group-level designation is not possible.
Queries containing an entered Restricted Statement will be blocked upon execution.
Query Annotation: Automatically records administrator-defined annotations when executing queries. If this feature is enabled, annotations are logged using the three templates below. Supported only for Redshift as of version 11.0.0.
User Name: {{userName}} – The display name of the user who executed the query.
Login ID: {{loginId}} – The login ID of the user who executed the query.
Executed From: {{executedFrom}} – The method used to execute the query, and only the Web Editor is recorded.
Member-based Connection Filtering: This feature allows you to filter connections in the Workflow DB Access Request form so that only specified connections are visible to certain users or groups, rather than exposing all connections.
Only users or groups added to Connection Members on the connection’s detail page will see that connection in the Workflow DB Access Request.
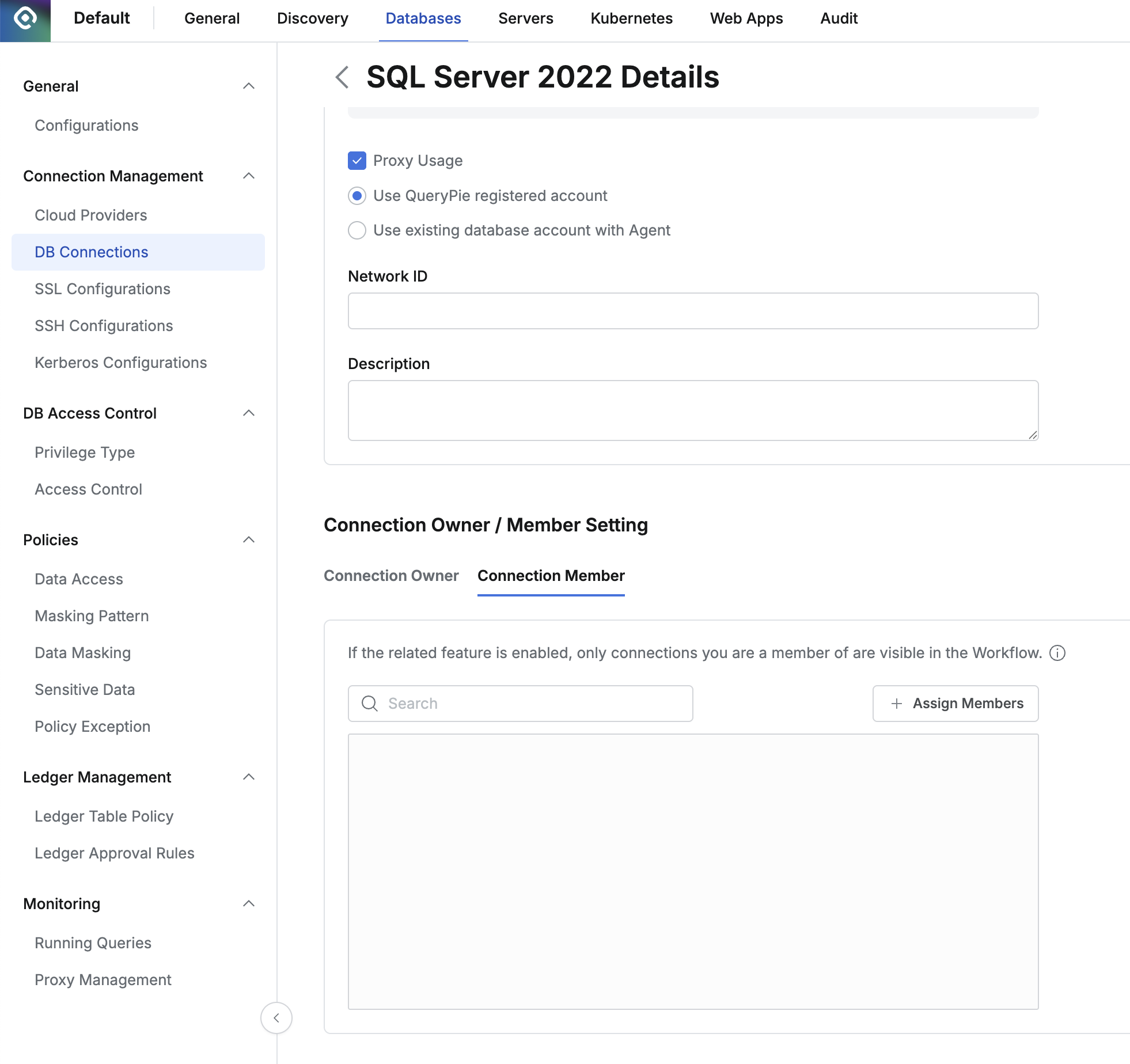
Assign specific users or groups to Connection Members on the detail page of a connection under Databases > Connection Management > DB Connections.
Queries blocked by a Restricted Statement policy will be blocked even if they have been approved via an SQL Request. Ensure that you do not input strings that would block queries essential for specific users who must be allowed to execute them.
Mandatory Reason Input for DB Operations
As of version 9.17.0, the functionality to enforce mandatory reason input for DB operations has been moved to connection-specific settings. For detailed configuration instructions, please refer to the Additional Settings in DB Connections documentation.
%201.png)