Granting and Revoking Kubernetes Roles
Overview
Administrators can grant or revoke roles with Kubernetes API access permissions to users or user groups.
Granting Kubernetes Roles
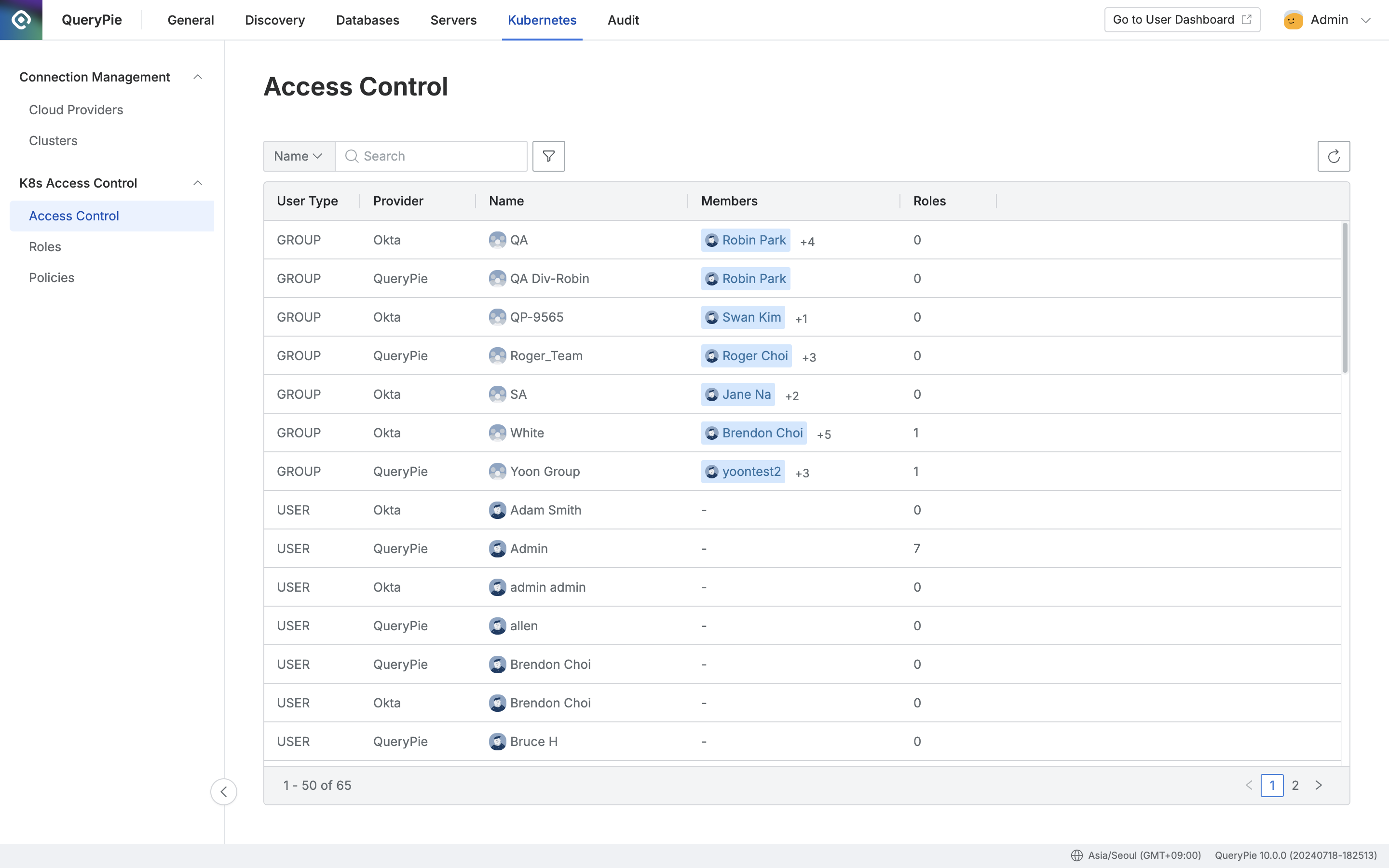
Administrator > Kubernetes > K8s Access Control > Access Control
- Navigate to Administrator > Kubernetes > K8s Access Control > Access Control menu.
- Select the user or user group to grant permissions to and navigate to the detail page.
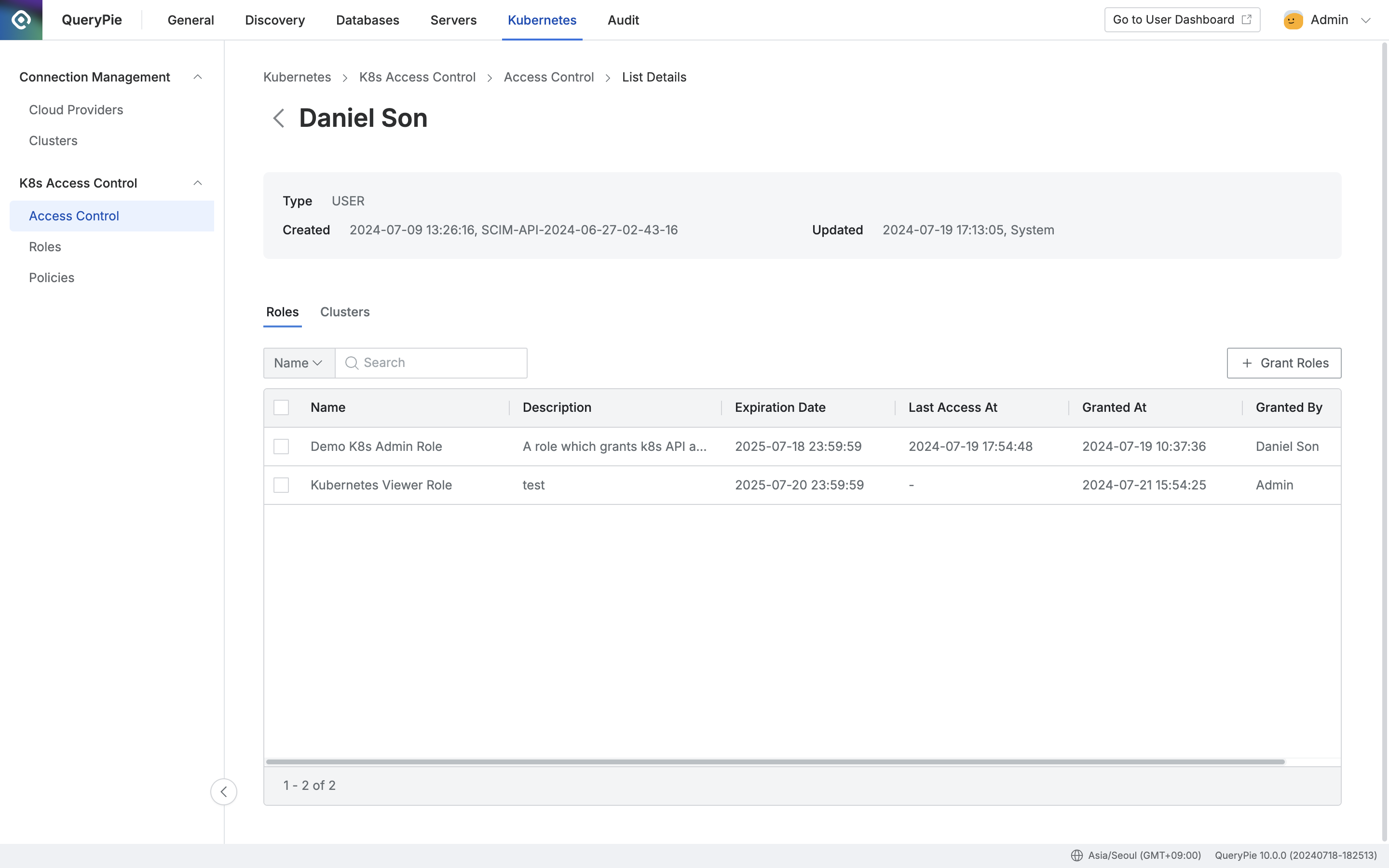
Administrator > Kubernetes > K8s Access Control > Access Control > List Details
- Click the
+ Grant Rolesbutton on the right side of the Roles tab, check the checkbox on the left of the Role to grant, and specify the expiration date.
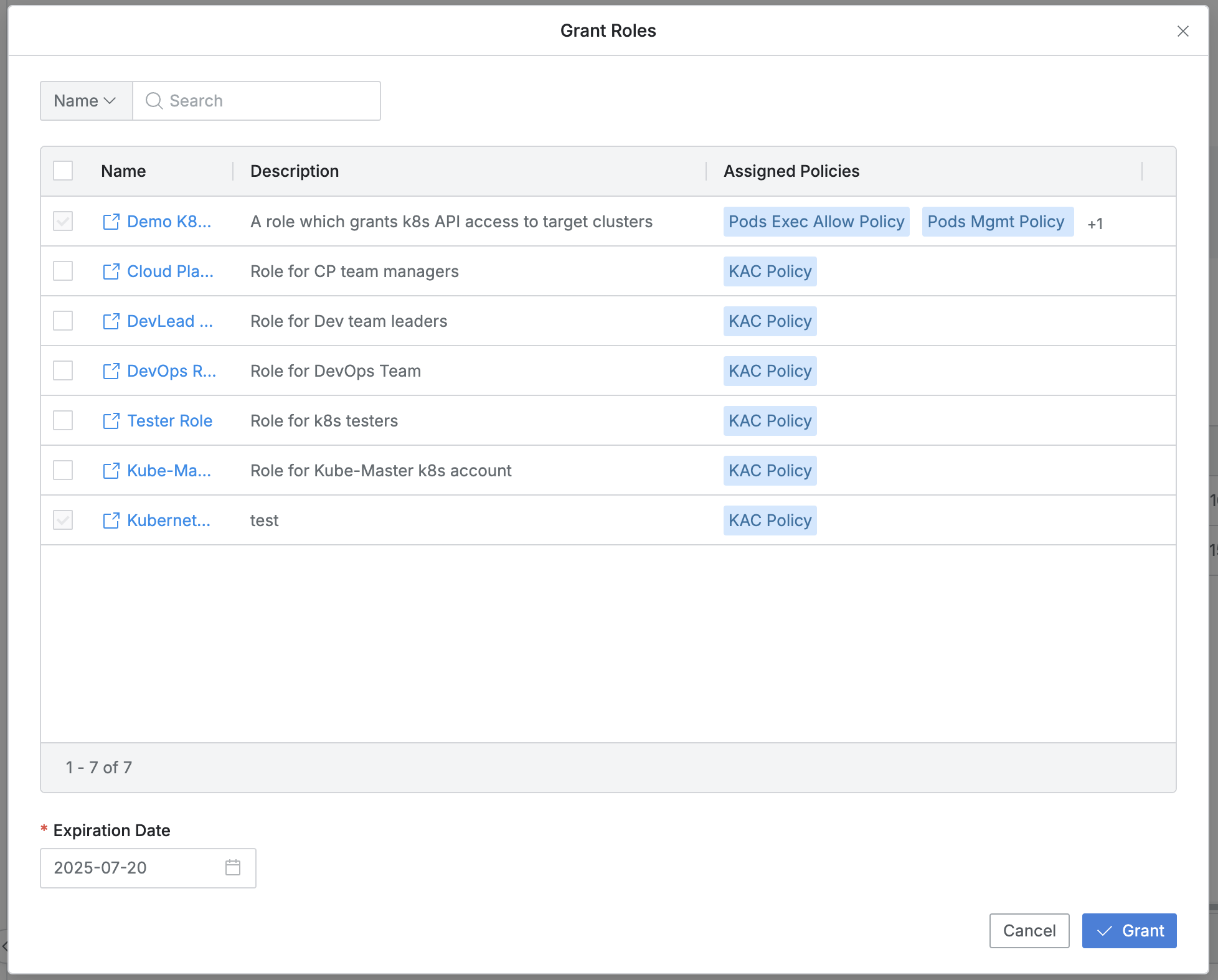
- You can search by Role name.
- Checkboxes for already assigned roles will be disabled.
- The list displays the following information for each policy:
- Name: Role name
- A new window link is provided to view the role information.
- Description: Detailed description of the Role
- Assigned Policies: Lists the assigned policies
- Name: Role name
- Expiration Date: The expiration date must be specified.
- By default, it is set to one year from the time of configuration, and can be set up to a maximum of one year.
- Click the
Grantbutton to assign the checked Role. - (Clicking the
Cancelbutton closes the modal without any changes.)
Revoking Kubernetes Roles
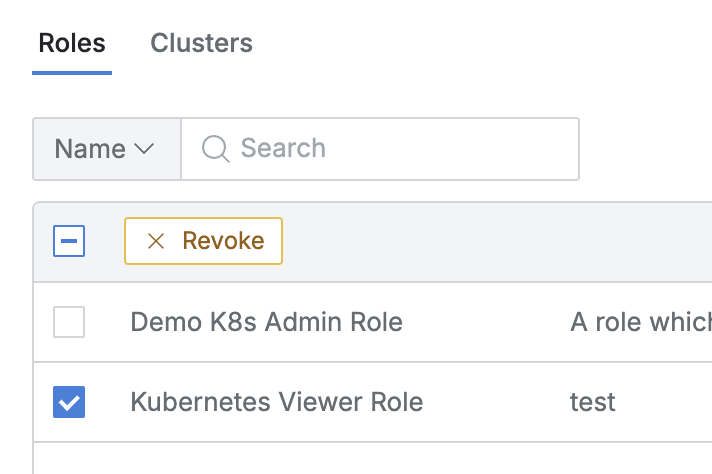
- Navigate to Administrator > Kubernetes > K8s Access Control > Access Control menu.
- Select the user or user group to revoke permissions from and navigate to the detail page.
- In the Roles tab, check the select all or individual selection checkbox, then click the
Revokebutton that appears in the column bar.
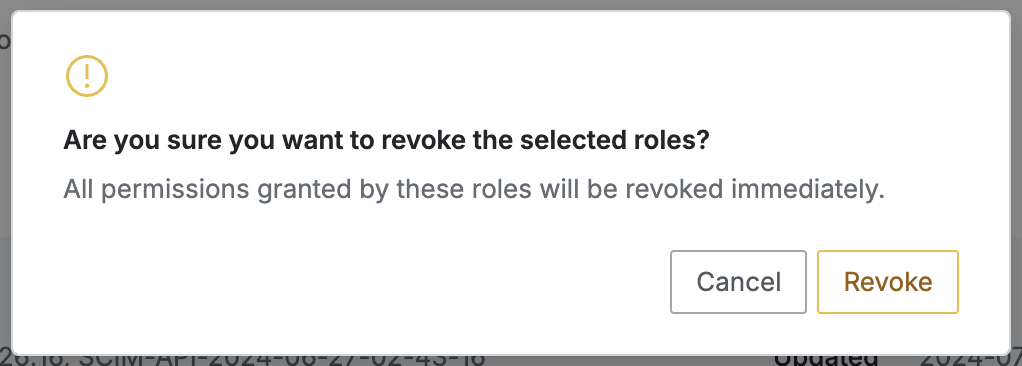
- When you click the
Revokebutton in the confirmation dialog, the selected role permissions are revoked from the user/group and removed from the list. - (Clicking the
Cancelbutton only closes the confirmation dialog.)
When a Role is revoked, all access permissions that were granted to users and groups through that role will be revoked.
Last updated on