Setting Kubernetes Roles
Overview
Role-Based Access Control (RBAC) based on Kubernetes roles within the organization is applied to allow or restrict user access to Kubernetes. You can assign configured Roles to users or user groups. Roles are used to combine multiple policies into a single role definition.
Assigning Role Policies
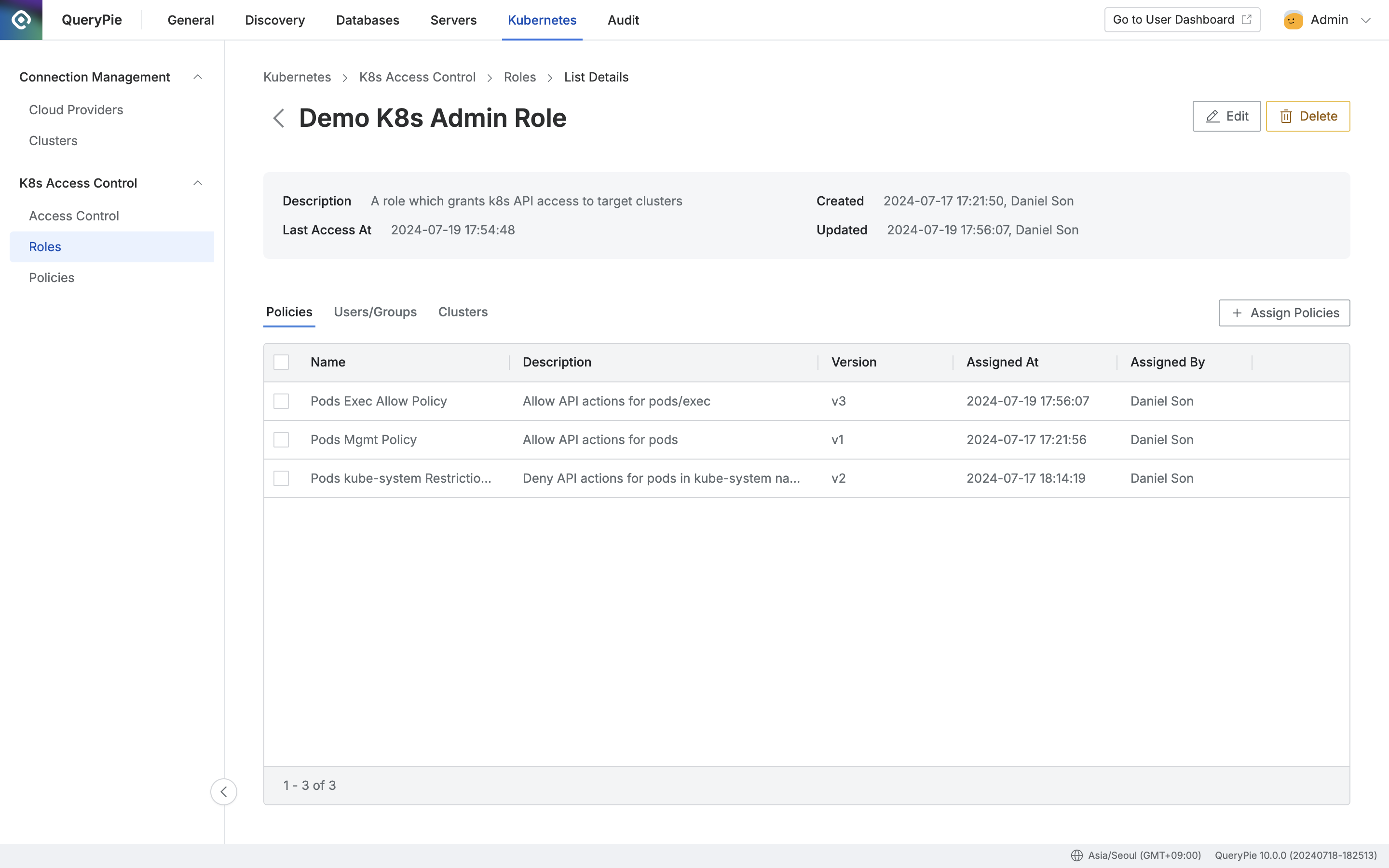
Administrator > Kubernetes > K8s Access Control > Roles > List Details
- Navigate to the Administrator > Kubernetes > K8s Access Control > Roles menu.
- Click on the target Role row in the Roles list to go to the details page.
- Click the
+ Assign Policiesbutton on the right side of the Policies tab. - Review the policies to assign, then check the checkbox on the left.
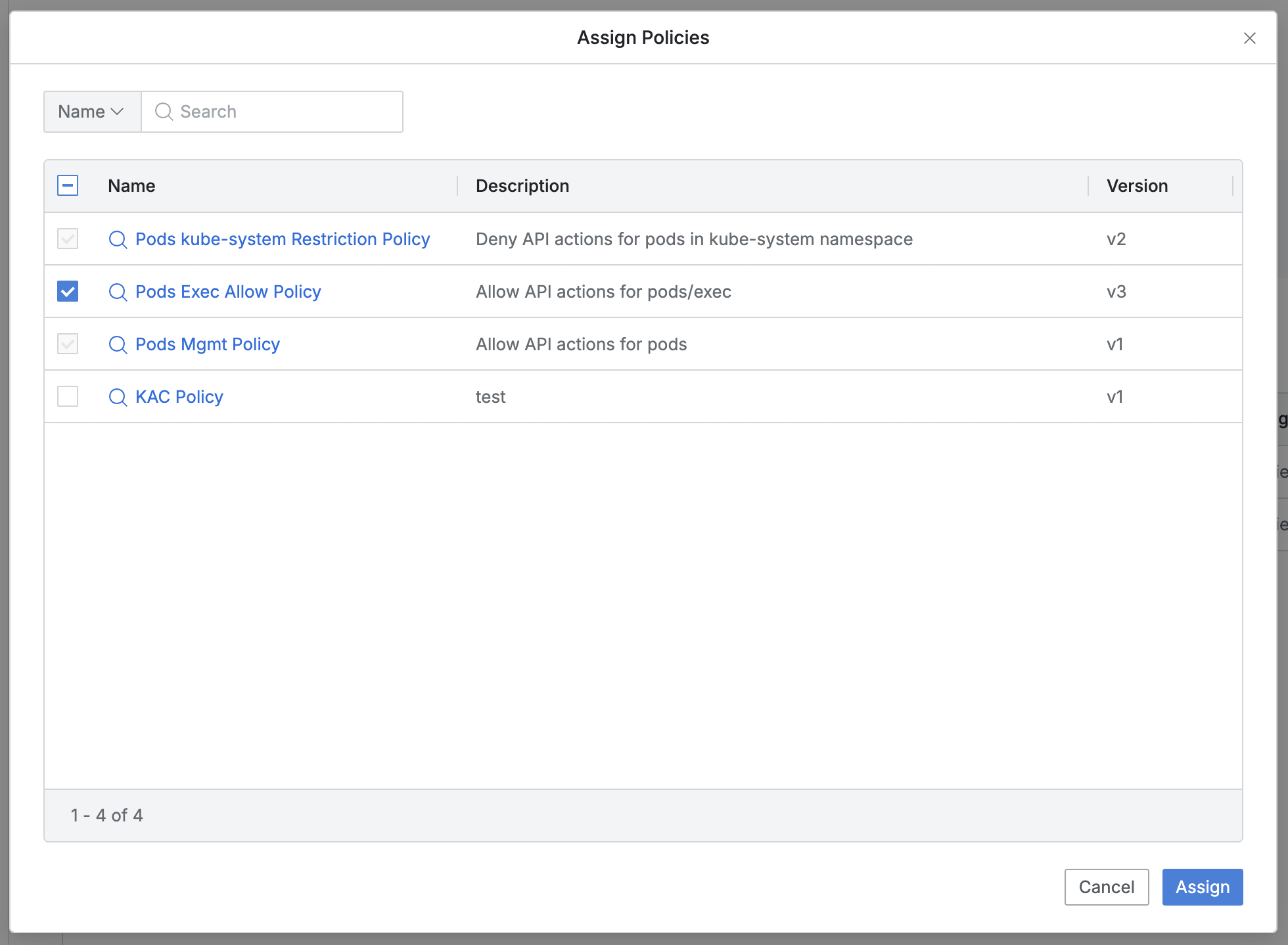
- You can search by policy name.
- Policies that are already assigned will have their checkboxes disabled.
- The list displays the following information for each policy:
- Name: Policy name
- A modal link is provided to view policy information.
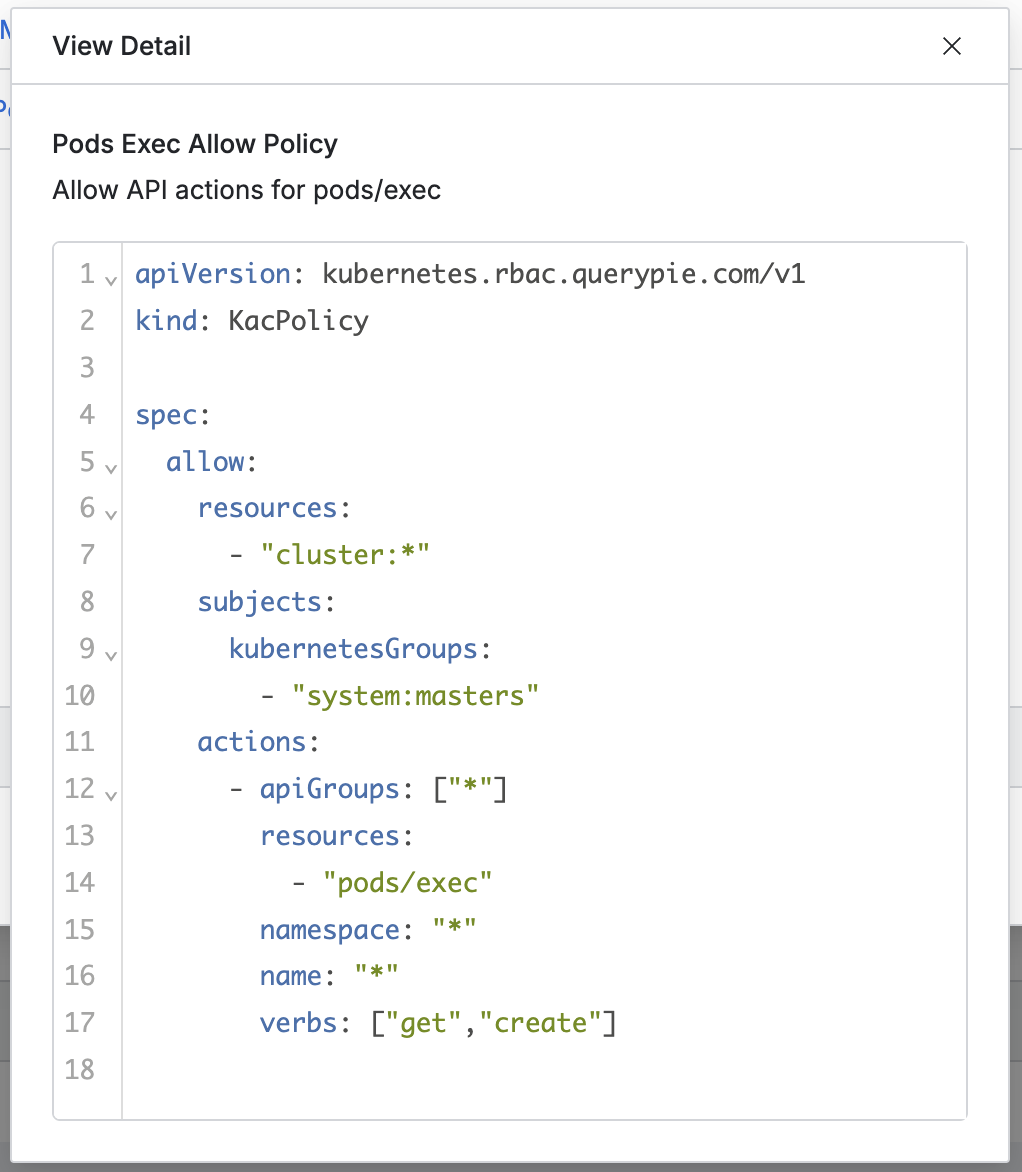
- A modal link is provided to view policy information.
- Name: Policy name
- Click the
Assignbutton to assign the selected policies. - (Clicking the
Cancelbutton closes the modal without any changes.)
Unassigning Role Policies
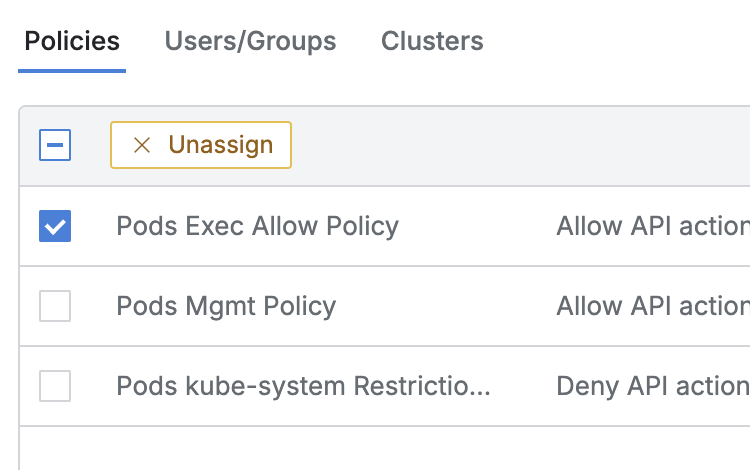
- Navigate to the Administrator > Kubernetes > K8s Access Control > Roles menu.
- Click on the target Role row in the Roles list to go to the details page.
- In the Policies tab, check the select-all or individual selection checkboxes, then click the
Unassignbutton that appears in the column bar.
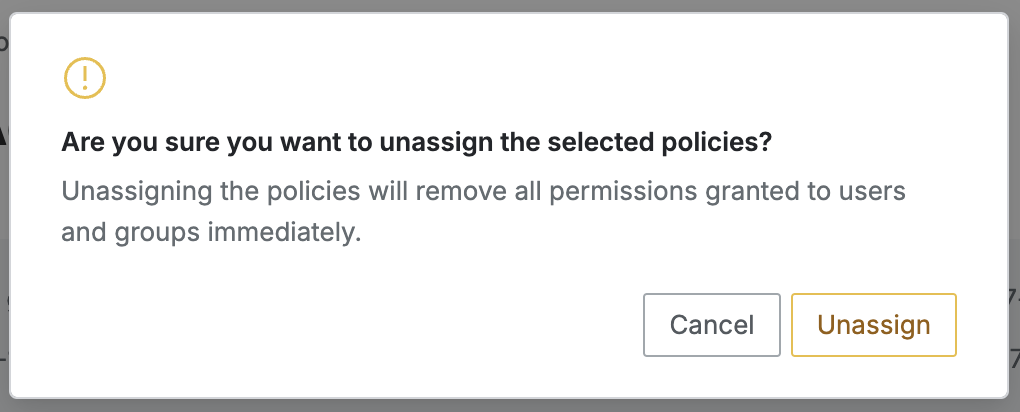
- When you click the
Unassignbutton in the confirmation dialog, the selected items are unassigned and removed from the list. - (Clicking the
Cancelbutton only closes the confirmation dialog.)
When a Policy is unassigned, all access permissions that were granted to users and groups through that policy will be revoked.
Last updated on